建議您使用以下瀏覽器觀看本網站,
以獲得最佳瀏覽效果。
Why an effective defense in layers approaches crucial for your cyber security strategy
With the ever-expanding list of cyber security threats, such as malware, ransomware, and insider threats, it has become a widely accepted notion among experts that it's not a question of if your company will experience a cyber attack, but rather when.

Do you know what you’re looking for?
What Attacks You Should Be Checking For
-
Malware
 This broad category encompasses spyware, viruses, trojans and worms. The common attribute is that all malware is developed solely to cause harm to computers, servers, or networks.
This broad category encompasses spyware, viruses, trojans and worms. The common attribute is that all malware is developed solely to cause harm to computers, servers, or networks. -
Ransomware
 One of the most common types of malware that gets a lot of media attention, ransomware denies the victim access to their data until they pay a ransom to release it.
One of the most common types of malware that gets a lot of media attention, ransomware denies the victim access to their data until they pay a ransom to release it. -
Phishing
 In a phishing attack, the criminal sends fraudulent emails containing malicious files or scripts to unsuspecting users. This type of attack exploits an organization’s point of vulnerability: its employees.
In a phishing attack, the criminal sends fraudulent emails containing malicious files or scripts to unsuspecting users. This type of attack exploits an organization’s point of vulnerability: its employees. -
Man-in-the-Middle Attacks
 These attackers exploit network security vulnerabilities by inserting themselves between someone’s device and the network, thereby redirecting information to themselves rather than the legitimate destination.
These attackers exploit network security vulnerabilities by inserting themselves between someone’s device and the network, thereby redirecting information to themselves rather than the legitimate destination. -
Denial-of-Service Attacks
 By flooding a system, server or network with traffic and requests, denial-of-service attacks can incapacitate a system or even take it completely offline, preventing it from fulfilling legitimate requests.
By flooding a system, server or network with traffic and requests, denial-of-service attacks can incapacitate a system or even take it completely offline, preventing it from fulfilling legitimate requests. -
Social Engineering Attacks
 In these attacks, the attacker uses social interaction and/or psychological manipulation to gain the trust of a human being, who then hands over login information or otherwise lets the attackers into the system.
In these attacks, the attacker uses social interaction and/or psychological manipulation to gain the trust of a human being, who then hands over login information or otherwise lets the attackers into the system.
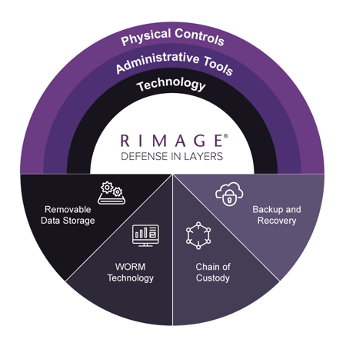
Defense in Layers Requires Proactive Focus
Rimage products and solutions cater to a variety of markets and applications. Select your market to learn how Rimage will integrate with your workflows, explore case studies, and more.
-
Physical Controls
 These are tools that control physical access to an organization’s IT systems, such as security teams, locked doors with managed access, biometrics, fences, video security, and the like.
These are tools that control physical access to an organization’s IT systems, such as security teams, locked doors with managed access, biometrics, fences, video security, and the like. -
Administrative Tools
 Employee training for both in-office and remote workforces as well as company policies, hiring practices and background checks are examples of administrative tools companies can use to protect data.
Employee training for both in-office and remote workforces as well as company policies, hiring practices and background checks are examples of administrative tools companies can use to protect data. -
Technology
 Organizations should include several different types of data security technology tools, such as:
Organizations should include several different types of data security technology tools, such as:
• Antivirus software
• Authentication/password security
• Encryption
• Firewalls
• Virtual private networks (VPNs)
• Multi-factor authentication
• Intrusion prevention software
Types of data security
Guarding against diverse forms of cyber attacks requires a comprehensive approach rather than relying on a single solution. At Rimage, we advocate for organizations to establish a robust Defense in Layers security posture by implementing a range of data security measures.
-
 Removable Data StorageOffline, removable data management. Data is stored on CDs, DVDs, Blu-ray, USB or other offline media to keep it out of the hands of cyber criminals.
Removable Data StorageOffline, removable data management. Data is stored on CDs, DVDs, Blu-ray, USB or other offline media to keep it out of the hands of cyber criminals. -
 WORM TechnologyWrite once, read many (WORM) technology. Data is written indelibly on removable management media so that it can be read any number of times, but never manipulated or changed.
WORM TechnologyWrite once, read many (WORM) technology. Data is written indelibly on removable management media so that it can be read any number of times, but never manipulated or changed. -
 Chain of CustodyChain of custody. Movement of data is tracked through its lifecycle to document each user that handles it.
Chain of CustodyChain of custody. Movement of data is tracked through its lifecycle to document each user that handles it. -
 Backup and RecoveryAir-gapped, offline backup and recovery. A copy of your data is kept offline and inaccessible from the internet so that cyber criminals can’t get to it.
Backup and RecoveryAir-gapped, offline backup and recovery. A copy of your data is kept offline and inaccessible from the internet so that cyber criminals can’t get to it.
Client Testimonials

Eric Power
Director of Strategic Initiatives

We’re not only managing our clients’ information from our technology platform, but we’re also managing it from an integrity standpoint. Our clients see offline and air-gapped backups as another safety check in their compliance, insurance and business continuity requirements to meet current and new government compliance needs.




